PowerBI reporting for Intune and AzureAD
Setting up Enterprise Mobility & Security for your organization is one thing. But what’s important is supporting and following it up after implementation. To help you in this, Microsoft offers extensive reporting for the EMS suite. By utilizing PowerBI we can create custom reports to visiualize your data..
PowerBI
PowerBI is the BI tool of Microsoft that can be used to visualize your data for easy reporting. PowerBI isn’t a free tool, but it’s included in an Office 365 Enterprise E5 license. A seperate PowerBI Pro license is available for 9,95 euro per user per month. If you want to test out the features before buying a license, a 60-day trail license is available.
In this blog I will go through two specific products: Intune and AzureAD.
Intune
Intune natively supports the ‘Intune Data Warehouse’, which can be used for reporting with all kind of tools. Nothing prohibits you to use a third party BI tool. But as we currently use PowerBI for all our reporting internally, I chose to use it for this bog. PowerBI also has some basic reports that can be used as a basis to create your own reports, which can be tailored to the needs of your organization.
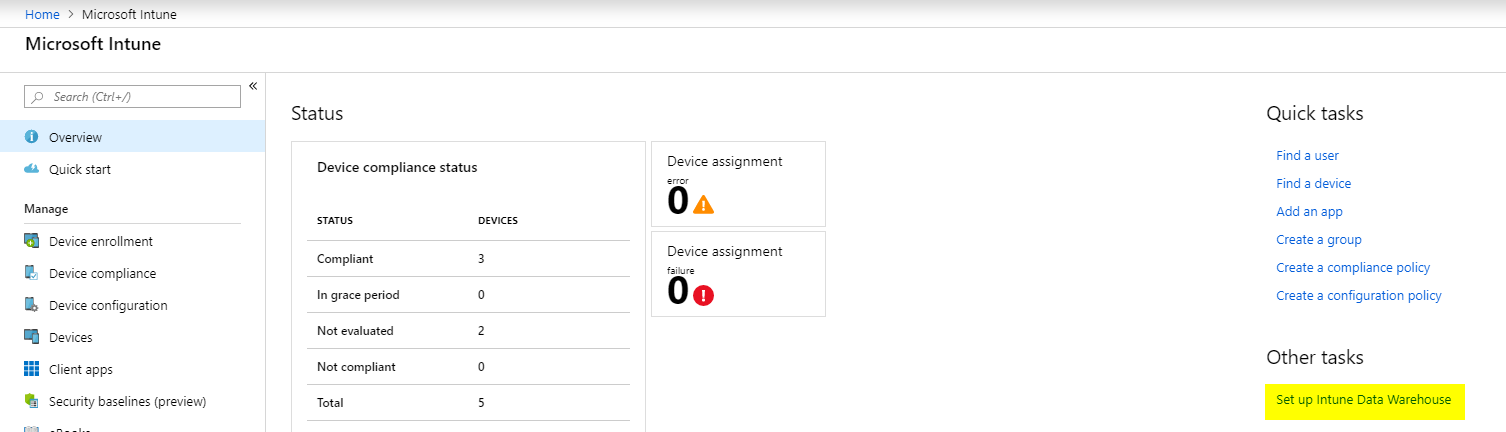
To get started, surf to your favorite adminlink and select ‘Intune’ in the left hand corner.
In the screen below select ‘Set up Intune Data Warehouse’.
Next up you have a few options. You can copy the custom URL to use in your third-party BI tool. Or you can follow the link to get the PowerBI app, that is the link we will follow.
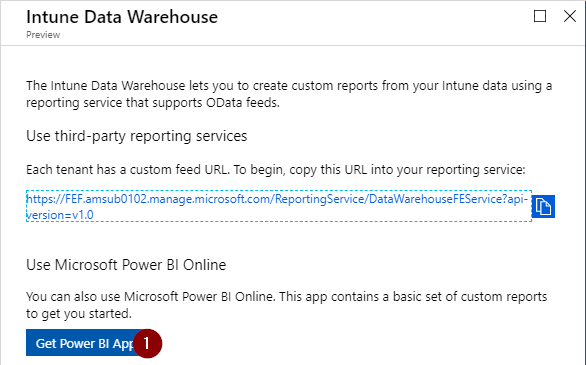
If you aren’t signed in to PowerBI already, you will be prompted to do so now.
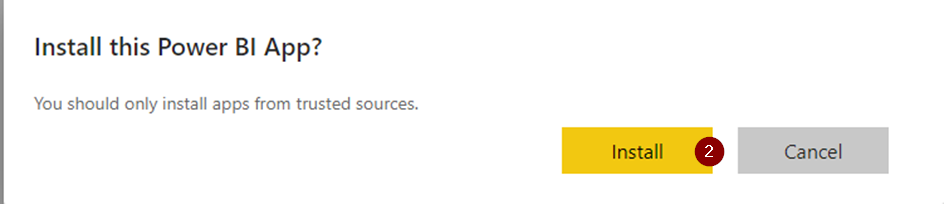
After signing in, you will receive the following prompt to install the PowerBI app. Click install and wait a minutes minutes for the app to finish installing.
After the installation you will receive a pop-up that the Intune Compliance Data app is installed. Click on it to open it.
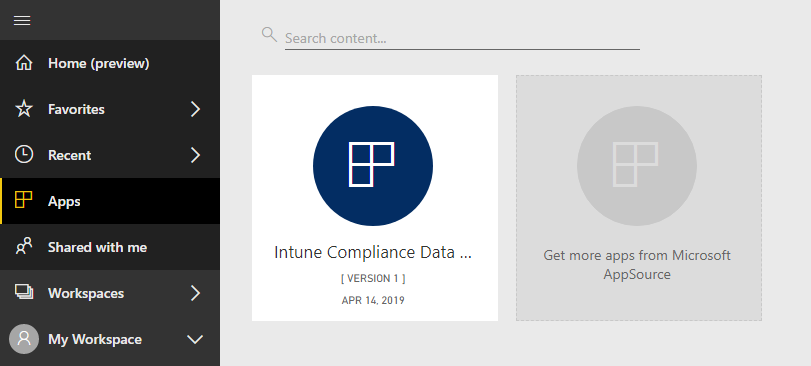
In the next screen, you will have the option to use sample data or use your own Intune data. Using sample data is a good choice if you don’t have an active Intune deployment and want to test out this feature. Because my tenant has data, I chose to connect to my Intune deployment.
Next up the PowerBI Compliance report will open.
You have four default tabs:
- Compliance Overview
- All Policy Breakdown
- Top noncompliant OS versions
- Compliance Data Table
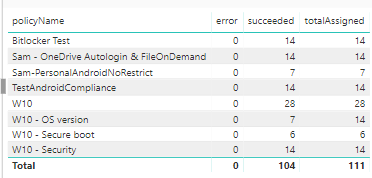
These are a few basic reports for compliance to get you up and running. You get create pretty extensive dashboards that will give you reports about your policy status and compliance status. With a few easy clicks, I can ceate a dashboards that show me the succesrate of my policies.
AzureAD
AzureAD is another part of the Microsoft EMS suite that has some custom dashboards preconfigured for you to use. Installing the AzureAD dashboard in your PowerBI environment is pretty simple.
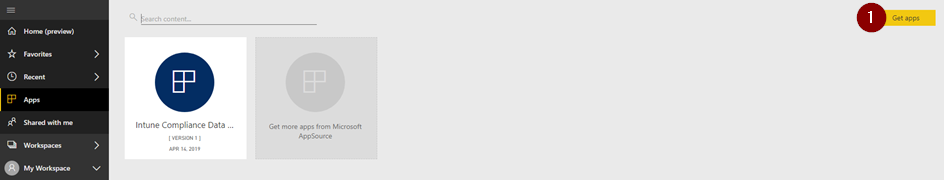
Go to your PowerBI homescreen, select apps and then select ‘Get Apps’ and the top right.
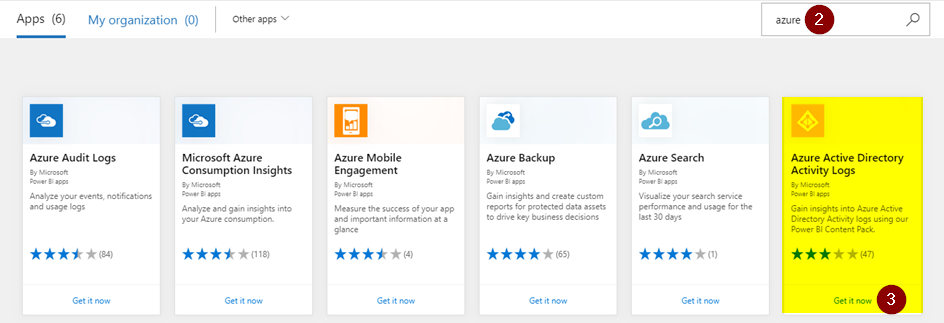
Search for Azure and you will see a whole lot of Azure dashboards (apps) available for use. We want the ‘Azure Active Directory Activity Logs’ app. Click it to install.
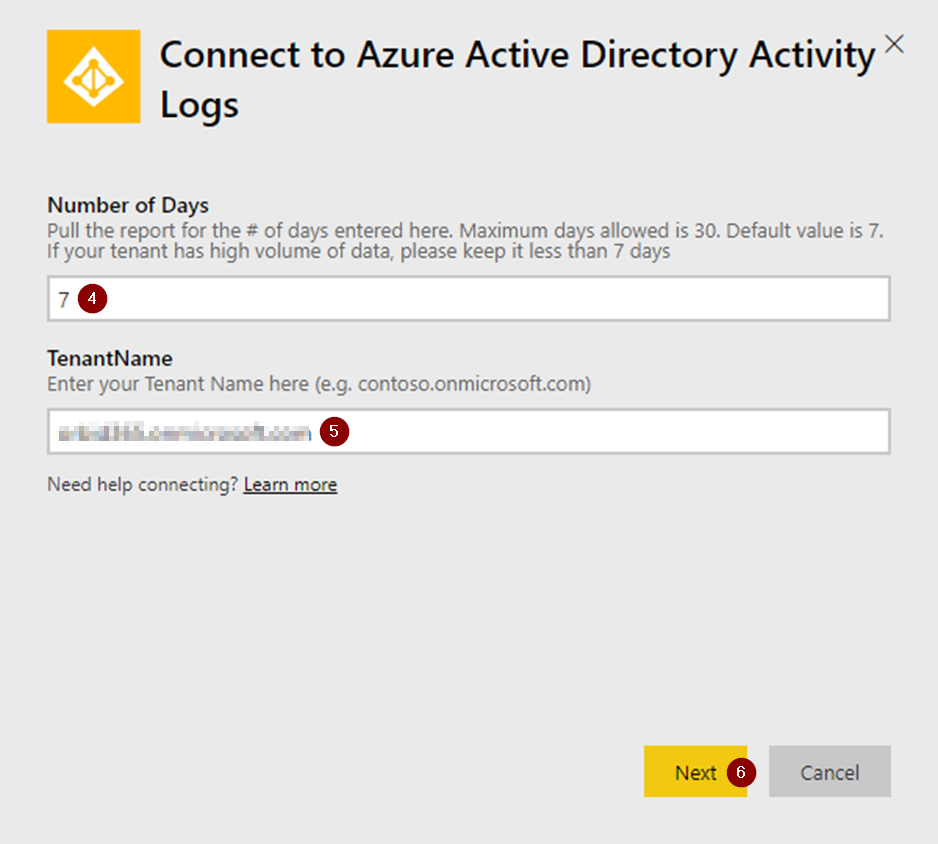
The app will require two parameters of you:
- How much data you want to analyze (in days). I chose 7 days but you can easily chose more (maximum is 30 days)
- Your tenant name (xx.onmicrosoft.com)
Fill in these parameters and click next.
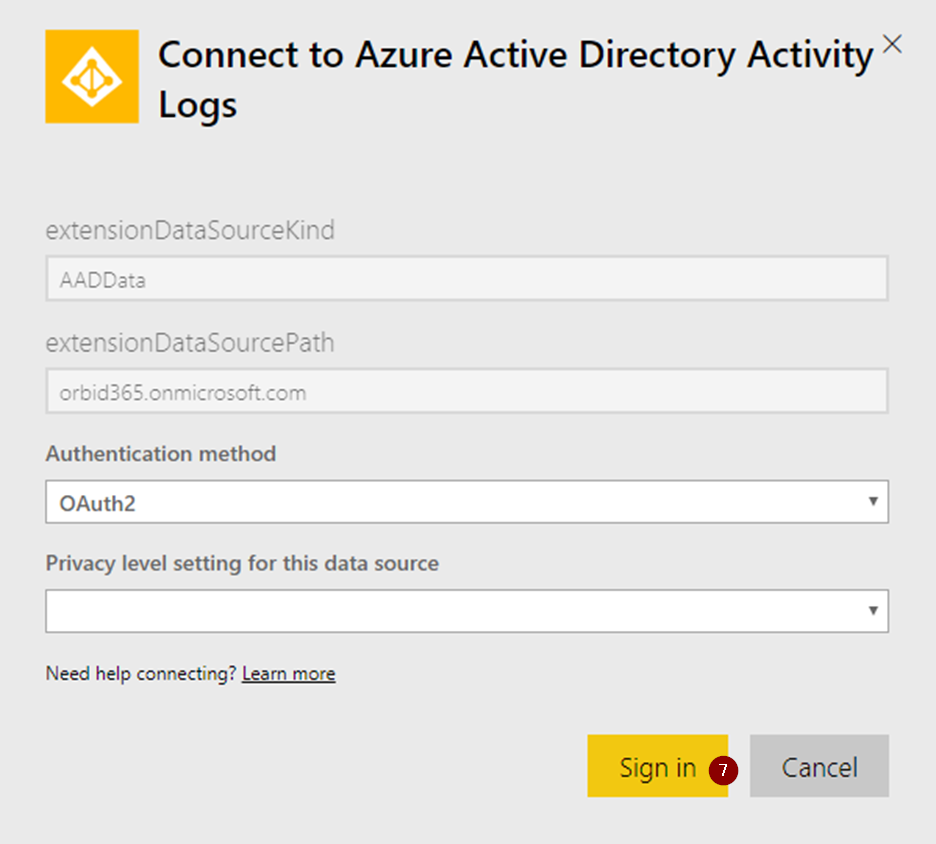
Next up, PowerBI will prompt us for an authentication method, OAuth2 is fine, click Sign In.
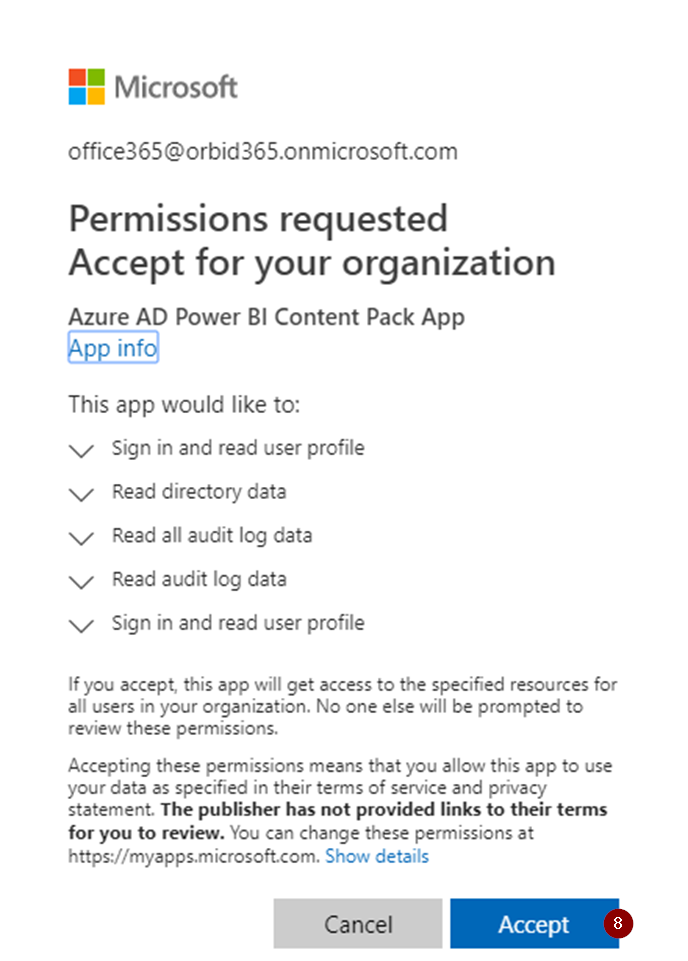
This Azure AD PowerBI app requires you to accept a few permissions. Specific, This means you will give it permissions to read AzureAD log data. Click ‘Accept’ to accept these permissions.
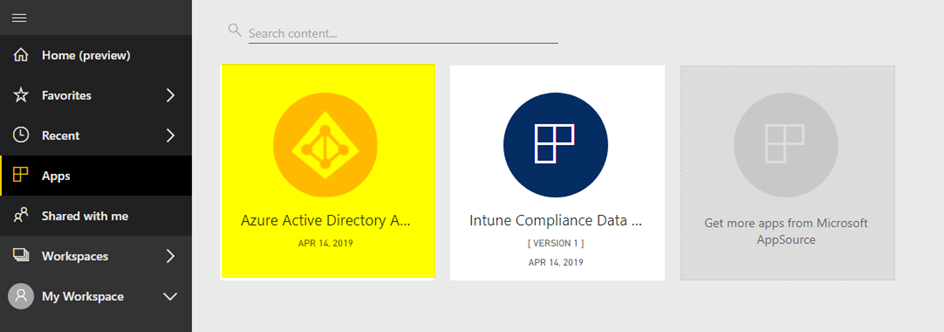
After accepting the permissions, wait for the app to finish installing. After installation, it will appear in your available apps.
Click the icon to open it.
After opening the app you are greeted with a dashboard with loads of data:
- Sign-in by location
- Total sign-ins
- Total users
- Application information
- SSPR information
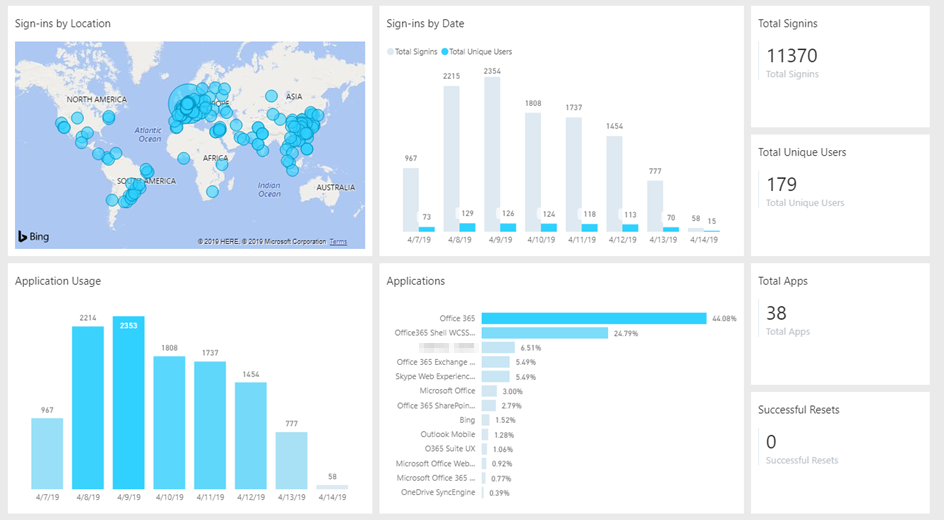
Everyone part of this dashboard supports a detailed view by clicking on it. For example we can click through on the ‘Sign-ins by Location’ where we can view a detailed overview.
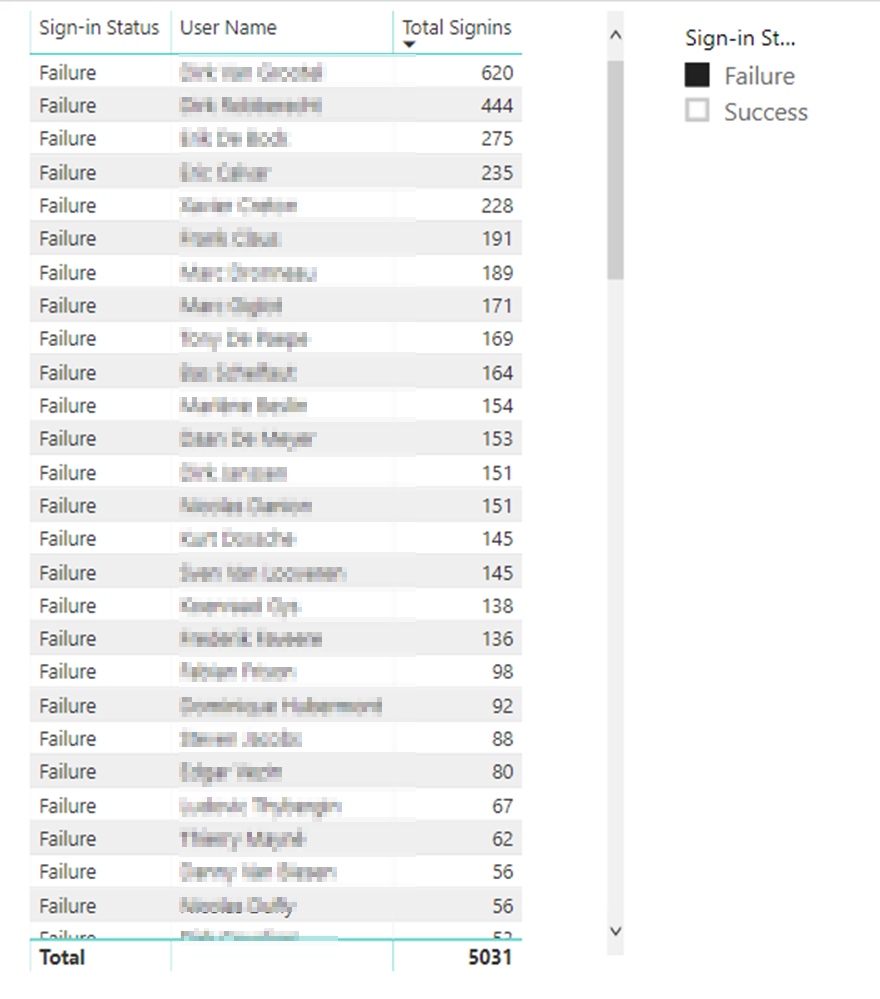
In this view, it is possible to filter on:
- User
- Device OS
- Device browser
- Sign-in Status (failure/success)
For this tenant, it showed me that were more failed than succesful sign-ins.

To better investigate this issue, I created my own custom view with a table and a slicer to see which users were having the most failed logins. In the table below, we saw a few key users that were being targeted.
With this information, we were able to better protection this environment.
The dashboard above is a very simple example of how you can use PowerBI to your advantage.
Summary
Both EMS and Intune generate lots of data for you to analyze. Using a good BI tool will make your job much easier when combing through logs. I strongly recommend playing around with these apps and creating your own dashboards.

I am a 22-year old cloud and automation enthusiast. My main focus is EMS, Powershell and Azure. My scripts can be found through my GitHub account: https://github.com/thijslecomte. I am currently blogging at http://365bythijs.be


Hi Thijs, strangely I don’t find the connector ‘Azure Active Directory Activity Logs’ in my powerBI.
Do we need special Azure licenses ? we have E3 +P1 and some P2.
Thanks
Chris
Hi Chris
For PowerBI you need a specific PowerBI license, or Office E5.
Do you have one of those?
Kind regards
Thijs
Hi,
I have Microsoft 365 E5 with PowerBI, but I don’t find this app
I have a PowerBI Pro license and an E5 license assigned. the dashboard is no where to be found. Is it still available?
I do not see it either and have read other reports online that they pulled it down.
I do not see that connector for Azure AD at all
Hello Everyone,
I Follow The Same Step but when i Search Azure Active Directory It Shows No results Found.